In this article we look at the vulnerabilities associated with enabling SQL Mail and look at ways to work around such security issues
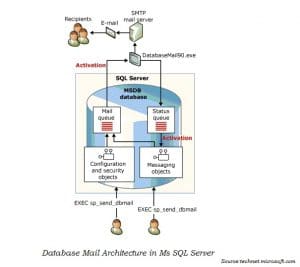 For SQL users, enabling an email database for replying to database queries is possible, since queries are handled by the database itself. However a minimum requirement for activating an email database in the application is to run SQL Server with a domain account having access to local admin privileges. However one of the drawbacks of using mail activated SQL databases is that anyone can request data, subject to restrictions put in place, from the system in the form of a query, and will get the information. Therefore limiting the amount of data that can be obtained is important. Another important thing to note about this feature is that, Query does not mean just a read – only request, but any legitimate SQL statement.
For SQL users, enabling an email database for replying to database queries is possible, since queries are handled by the database itself. However a minimum requirement for activating an email database in the application is to run SQL Server with a domain account having access to local admin privileges. However one of the drawbacks of using mail activated SQL databases is that anyone can request data, subject to restrictions put in place, from the system in the form of a query, and will get the information. Therefore limiting the amount of data that can be obtained is important. Another important thing to note about this feature is that, Query does not mean just a read – only request, but any legitimate SQL statement.
Few of the Most Common Vulnerabilities Faced in SQL Server
- Since it does not only consider a query as a read only request but a valid SQL statement, a user can not only use it for obtaining information but also for processing insert, updating, deleting commands, and creating and modifying objects.
- The reply-to-sender approach of the feature does not make any attempt to verify the requester or to even check for necessary authorization. However, you can prevent this from happening by enabling authentication and authorization checks for SQL mail query, but this still won’t guarantee any integrity or confidentiality.
- The security of the feature is badly handled, and is based entirely on ignorance of the intruder. Therefore, an intelligent intruder, with the very basic knowledge of the mail accounts, can send a query to be implemented in the target database.
How can you Keep the SQL Server Email Vulnerabilities at Bay
 As mentioned already, the security of the feature is badly handled and based on ignorance of the attacker, the user can literally hope that attacker is not aware of system vulnerabilities. It does not just end here, there is a lot more the user can only wish for – the attacker does not know of the implemented and vulnerable databases, the account which can be used for putting up queries etc. All the barriers to vulnerabilities of the mail database feature stem from how unaware the attacker is. One of the suggested tip to to protect mail database from unauthorized access would be to not have really obvious names for the accounts used. Attackers can simply guess the privileged accounts if they are too obvious. Another thing to keep in mind is, if you are making multiple databases mail enabled; add separate accounts for each database. Last but not the least keep a SQL Server fix tool handy to deal with incidents of data corruption.
As mentioned already, the security of the feature is badly handled and based on ignorance of the attacker, the user can literally hope that attacker is not aware of system vulnerabilities. It does not just end here, there is a lot more the user can only wish for – the attacker does not know of the implemented and vulnerable databases, the account which can be used for putting up queries etc. All the barriers to vulnerabilities of the mail database feature stem from how unaware the attacker is. One of the suggested tip to to protect mail database from unauthorized access would be to not have really obvious names for the accounts used. Attackers can simply guess the privileged accounts if they are too obvious. Another thing to keep in mind is, if you are making multiple databases mail enabled; add separate accounts for each database. Last but not the least keep a SQL Server fix tool handy to deal with incidents of data corruption.
A Word of Caution
SQL injection is another common technique used by hackers to get access to the database, it makes use of a trial-and-error method, by using web URLs to introduce modifications, and then gain access to the database. SQL Mail database as compared to SQL injections is easier to crack, and preferred more by the attackers, it is not as intensive and time consuming as SQL injections, therefore always ensure your accounts are protected and user authentication and authorization is enabled for the feature.
Author Introduction:
Victor Simon is President & Chairman of DataNumen, Inc., which is the world leader in data recovery technologies, including repair accdb corruption and sql recovery software products. For more information visit www.datanumen.com