1. Introduction
In today’s rapidly advancing digital age, the need for understanding, investigating, and securing electronic data is more crucial than ever. Enter the realm of computer forensics, a specialized discipline that plays an essential role in extracting valuable information from various digital sources. The technology is vital for solving a multitude of cases, ranging from corporate espionage to criminal investigations.
The importance of computer forensics isn’t merely confined to the legal arena; it’s a multidisciplinary field that extends its roots into corporate governance, cybersecurity, and even into the private sector for personal matters. Whether it’s tracking down cybercriminals, protecting corporate assets, or preserving crucial data, computer forensics offers a range of solutions tailored to modern challenges.
As the field continues to evolve with new methodologies, tools, and ethical considerations, a comprehensive understanding becomes indispensable. This article aims to serve as a thorough introduction to computer forensics technology, covering its definition, history, importance across various fields, principles, methodologies, types of digital evidence, legal aspects, and much more.
Join us as we delve deeper into this fascinating world, illuminating the vital components that make computer forensics an indispensable tool in our digital society. Whether you are a law enforcement officer, a cybersecurity expert, or just an interested individual, there’s something for everyone to learn.
2. Definition of Computer Forensics
Computer forensics, often referred to as digital forensics, is the practice of collecting, analyzing, and preserving electronic evidence in a way that is legally admissible. At its core, the discipline aims to reconstruct a digital crime scene, facilitating the understanding of the “what, when, how, and by whom” regarding questionable or illegal activities involving digital systems. The primary objectives include establishing timelines, recovering lost data, and providing substantial evidence for legal proceedings.
For example, a criminal deleted a ransom email in Outlook. The police can use DataNumen Outlook Repair to recover that email and use it as evidence in court.
In more practical terms, computer forensics is often the go-to method for investigating digital fraud, unauthorized data access, and various types of cybercrime. It is not limited to just computers but extends to other digital devices like smartphones, tablets, and even cloud storage services, reflecting the diversity and complexity of modern technology.
But computer forensics is not merely a reactive tool; it also has proactive applications. For instance, companies employ forensic techniques to test their network vulnerabilities, thereby taking preventive measures to avoid future security breaches. These proactive measures demonstrate how deeply embedded and essential computer forensics is in various aspects of digital life.
To sum it up, computer forensics provides a systematic approach for digging deep into electronic devices and networks to extract meaningful information, whether to solve a crime, safeguard an organization, or even protect individual users. It marries technology with legal processes, making it a cornerstone in modern investigative methods.
3. History and Evolution of Computer Forensics
The field of computer forensics has seen a fascinating evolution that mirrors the rise and spread of technology itself. Originating in the late 1970s and early 1980s, the discipline started taking shape as computers became more prevalent and, consequently, as crimes involving digital devices began to emerge. Law enforcement agencies soon recognized the need for specialized skills to handle electronic evidence, which led to the formalization of computer forensics as a unique field.
In the 1990s, with the explosion of the internet, computer forensics gained unprecedented importance. Cybercrimes like hacking, identity theft, and online fraud surged, calling for robust forensic methodologies to investigate and mitigate these issues. As software systems advanced, so did forensic tools, techniques, and best practices, leading to the development of specialized software for data recovery, analysis, and reporting.
The early 2000s marked another pivotal period, with the rise of mobile computing and smartphones. Suddenly, computer forensics wasn’t just about desktops or mainframes; investigators had to adapt their skills to include mobile devices, cloud storage, and even IoT devices. The field expanded in scope and complexity, requiring a new set of approaches and tools to deal with this broader spectrum of electronic evidence.
In the modern era, we see the integration of artificial intelligence and machine learning techniques into computer forensics. These technologies aid in data analysis, pattern recognition, and even predictive forensics, which aims to forecast potential future activities based on past behavior. As we move deeper into the age of big data, cybersecurity, and interconnected devices, the role of computer forensics will only continue to grow, becoming an increasingly integral part of our digital world.
4. Key Techniques and Methodologies in Computer Forensics
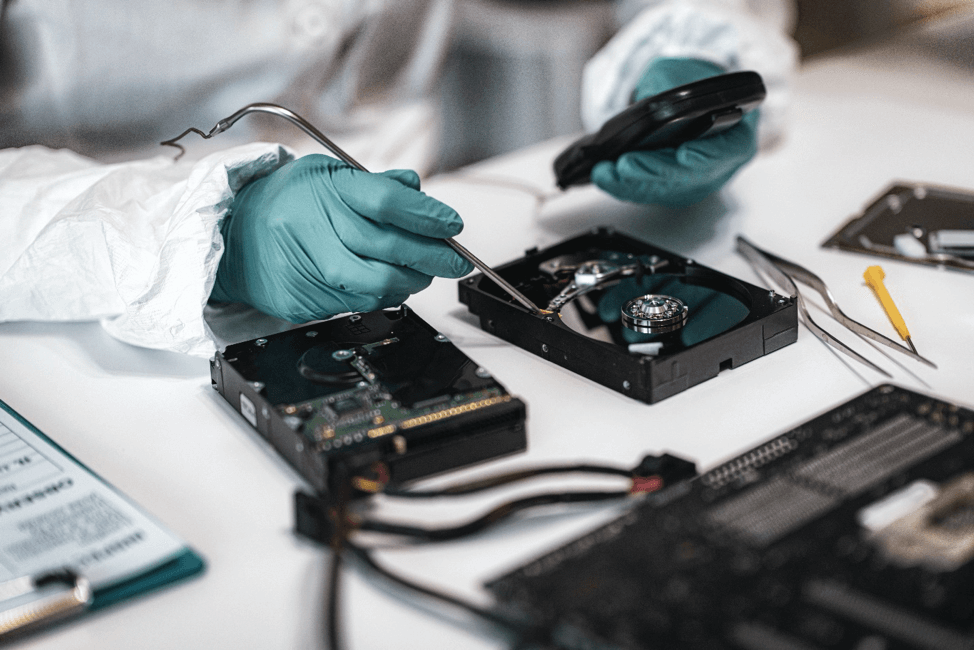
In computer forensics, a variety of techniques and methodologies are employed to achieve reliable and legally admissible results. One of the foremost techniques is data acquisition, which is the process of gathering digital evidence from various sources. This involves not just copying files but often creating a bit-for-bit image of the storage medium, ensuring that even deleted or hidden data can be analyzed. Proper chain-of-custody procedures are essential during this stage to maintain the integrity of the evidence.
Another crucial area is data analysis, which can be broken down into several sub-processes like file artifact analysis, network traffic examination, and timeline analysis. Forensic experts use specialized software tools to sift through large volumes of data, identifying pertinent evidence and establishing timelines. This phase often involves parsing different file formats, decrypting encrypted data, and even reconstructing fragmented data to get a clearer picture of activities under investigation.
Data recovery is also an essential aspect, especially when dealing with deleted or encrypted files. Through various techniques such as file carving and data scraping, investigators can retrieve crucial pieces of information that may otherwise have been considered lost. This process is often vital in cases involving fraud, information theft, or any criminal activity where evidence has been deliberately erased. DataNumen SQL Recovery is widely used in recovering SQL Server databases that are permanently deleted by criminals.
The final piece of the puzzle is reporting and documentation. This involves compiling all findings in a coherent and structured manner for presentation in court or other legal settings. Here, the focus is not just on the technicalities but also on making the information understandable to non-technical stakeholders like lawyers, judges, and juries. Proper documentation ensures that the evidence is not only accurate but also legally admissible, which can make or break a case.
5. The Difference Between Computer Forensics and E-Discovery

Computer Forensics focuses on the identification, preservation, extraction, and documentation of electronic evidence, often for criminal or civil litigation. Forensics experts analyze data at a binary level and are equipped to retrieve information, even if it has been deleted or altered. They aim to establish a chain of custody for the electronic evidence, ensuring it is admissible in court. Techniques used in computer forensics can delve into the depths of a computer system, identifying how data was created, modified, or deleted.
E-Discovery, on the other hand, is a broader practice usually occurring in the litigation process, but it is not confined to legal investigations. E-Discovery involves identifying, collecting, and producing electronically stored information (ESI) like emails, documents, databases, voicemails, etc., that are relevant to a legal case. Unlike forensics experts, E-Discovery professionals are typically not concerned with the in-depth analysis of how or why the data was created. Their primary focus is on ensuring that relevant information is retrievable and organized in a way that it can be reviewed for legal proceedings.
Another key difference lies in the scope of work. Computer forensics is usually more targeted, focusing on specific incidents or points of data. E-Discovery, however, often involves voluminous amounts of data and is broader in scope, frequently needing to comply with legal requirements for information management and preservation.
In summary, while both Computer Forensics and E-Discovery aim to retrieve and analyze electronic information, their approaches, objectives, and scopes differ significantly. Knowing which approach is more appropriate for a given situation is crucial for effective data management and legal compliance.
6. Ethical and Legal Considerations in Computer Forensics
Ethical and legal considerations form the backbone of any computer forensic investigation. Ensuring compliance with legal frameworks is not merely an option but a necessity. Failure to adhere to legal guidelines can lead to the disqualification of evidence, rendering the whole forensic process useless in a court of law. Adherence to laws, such as search and seizure protocols or data protection acts, is vital to validate the integrity of an investigation.
Equally important is the ethical component, which often overlaps with legal issues. Consent to access and analyze a system is a foundational ethical concern. Unauthorized intrusion, even for an investigation, can create serious ethical dilemmas and can also be unlawful. Forensic experts must always operate under appropriate legal permissions, which usually means having explicit consent or a warrant before starting any forensic examination.
Another cornerstone of ethical practice is objectivity. A forensic analyst should not have any vested interests in the outcome of an investigation. This is vital for maintaining the credibility of the findings, as bias can quickly undermine an entire investigation. Objectivity ensures that an analyst will report facts, regardless of how they might affect the parties involved, ensuring that justice is the ultimate goal.
Transparency and documentation round out the ethical and legal must-haves. Every step of the forensic process should be transparent and well-documented to stand up to scrutiny, either from opposing legal teams or from internal audits. This rigorous documentation process also aids in peer review, allowing other experts in the field to validate the methods and conclusions, reinforcing the strength of the findings.
7. Challenges and Limitations in Computer Forensics
Computer forensics, while incredibly powerful, is not without its set of challenges and limitations. One of the most pressing issues is the sheer volume of data that forensic experts have to sift through. With storage capacities consistently increasing, the amount of data to be analyzed can be overwhelming. This not only makes the forensic process time-consuming but also requires significant computational resources.
The rise of encryption technologies also poses a significant hurdle. While encryption is great for protecting privacy, it makes the forensic analysis extremely complicated. Even with powerful algorithms and computational tools at their disposal, decrypting secured data is a slow and arduous process that is not always successful. Forensic analysts need to stay ahead of the curve in cryptography to remain effective.
Another concern is the increasing sophistication of cybercriminal techniques. Malicious actors are constantly improving their methods to evade detection, employing a variety of tactics ranging from data obfuscation to the use of decentralized networks and anonymous browsing. Keeping up with these advancements requires ongoing training and research, putting pressure on forensic analysts to continuously update their skillsets.
Lastly, jurisdictional issues can often complicate matters. In the era of globalized communications and data storage, jurisdiction becomes a gray area. Laws and regulations governing computer forensics may differ from one country to another, making international cooperation difficult. Determining the jurisdiction under which a particular piece of evidence falls can be a significant logistical and legal challenge.
8. Future Trends and Emerging Technologies in Computer Forensics
The landscape of computer forensics is ever-evolving, thanks to rapid technological advancements. One of the most prominent trends is the increasing focus on cloud forensics. With more data being stored in the cloud, forensic experts must adapt their methodologies to gather evidence from these decentralized platforms. Traditional data acquisition techniques often fall short, and newer, more specialized tools and approaches are being developed to tackle this challenge.
Another significant shift is in the area of mobile forensics. With smartphones becoming ubiquitous and increasingly sophisticated, they are often key evidence sources in criminal and civil investigations. The unique set of challenges they present—ranging from varied operating systems to encrypted data storage—requires constant adaptation in forensic methodologies. Techniques such as live data acquisition from mobile devices are gaining importance, offering a glimpse into real-time user activities.
Artificial intelligence (AI) and machine learning are also beginning to make their mark. These technologies have the potential to automate various aspects of data analysis, making it quicker and more efficient. Predictive modeling can help investigators focus on critical data points, cutting down the amount of redundant information to sift through. However, the use of AI also raises ethical concerns, particularly when it comes to bias and reliability, requiring a balance between automation and human expertise.
Lastly, the emergence of quantum computing poses both challenges and opportunities. While its processing capabilities could revolutionize data decryption, making current encryption methods obsolete, it could also offer new, more secure ways of storing data. This dichotomy represents a new frontier that forensic experts will soon have to navigate, and preparations for this are already underway in the form of quantum-safe cryptographic algorithms.
9. Conclusion and Recommendations
Computer forensics has come a long way, transitioning from a niche discipline to a cornerstone in modern criminal and civil investigations. As technology continues to evolve, so too will the methods, tools, and challenges faced by forensic experts. While advancements are promising, they also necessitate an adaptive, educated, and ethically responsible community of professionals to navigate the ever-changing landscape effectively.
To keep pace with this fast-evolving field, continuous learning is essential. Academic and professional training programs should be sought to acquire new skills and keep up-to-date with the latest methodologies. Certifications from reputable organizations can help forensic professionals stand out and validate their competencies, which is especially critical in such a specialized field.
For organizations, investing in robust forensic tools and infrastructure is not optional but a requirement to perform investigations with speed and accuracy. Whether it’s hardware or software solutions, ensuring that you have the right technology at your disposal is key to success. Moreover, collaboration across different domains of cybersecurity, data analysis, and law enforcement can facilitate a more holistic approach to investigations.
Finally, ethics and legality should never be compromised. Adhering to guidelines, respecting privacy, and following the law are not just professional requirements but moral obligations. Non-compliance could result in compromised investigations and legal repercussions, thereby emphasizing the need for integrity in all operations.
Author Introduction:
Vera Chen is a data recovery expert in DataNumen, Inc., which is the world leader in data recovery technologies. For more information visit www.datanumen.com